- New users created through Okta will also be provisioned in Isolocity.
- Roles in Isolocity will adhere to the user’s membership to the groups in Okta that Isolocity recognizes. See “Isolocity Roles in Okta” section.
Okta Configuration Guide
Supported Features
Prerequisites
- Contact us at support@isolocity.com to enable users in your organization to log into Isolocity using their Okta credentials.
- We will need the following information:
- Your logo (pref png format)
- Your Okta issuerUrl, e.g. https://company-name.okta.com/oauth2/default
- The minimum user role when users log in to Isolocity for the first time
- The default Team for the user
- Okta ClientID (once available from your Okta console)
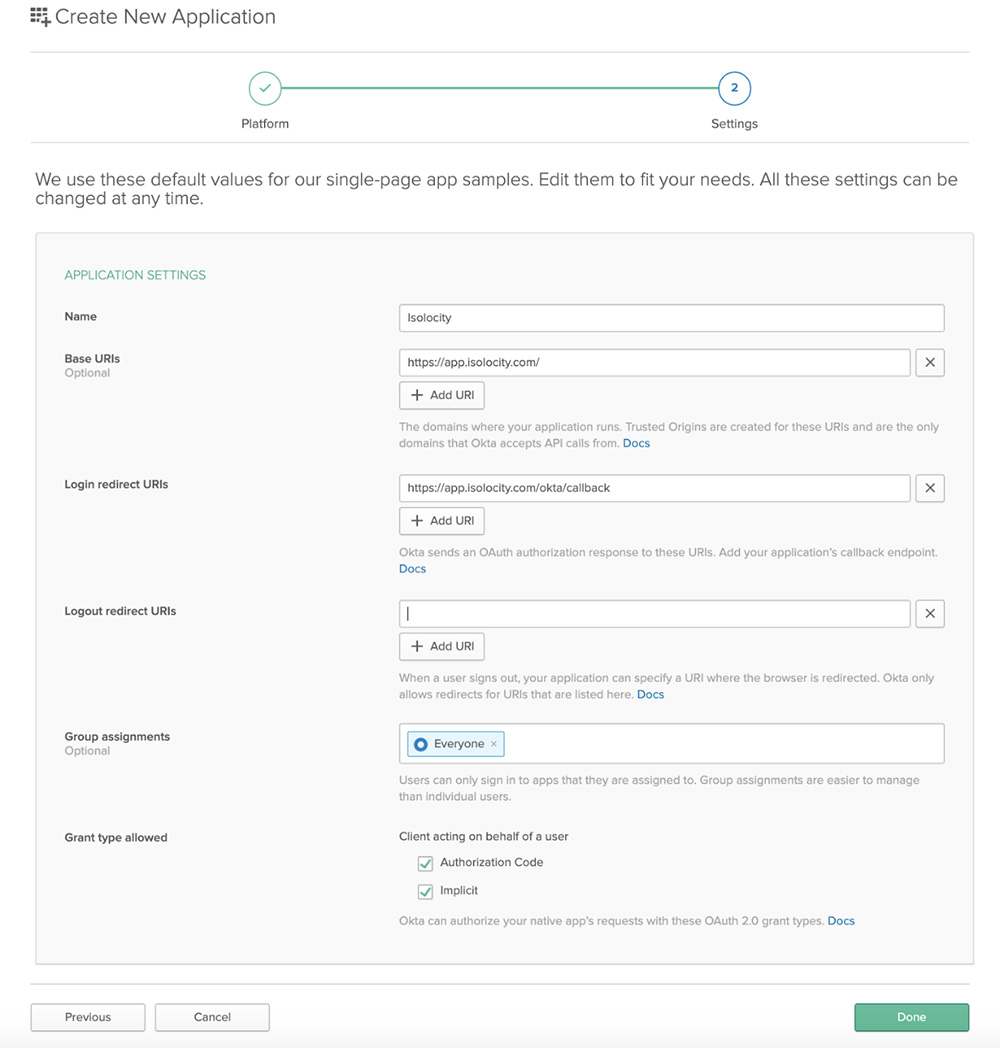
- Login with admin privileges to your organization’s Okta account and add the Isolocity application: Click Applications > Add Application > Single-Page App (SPA).
- Click Next, then enter the following information:
- Name: Isolocity
- Base URI: https://app.isolocity.com
- Login Redirect URI: https://app.isolocity.com/okta/callback
- Logout Redirect URI: leave blank
- Leave the other defaults and click Done
- Click on the application just created. Provided on the General tab, kindly provide us your ClientID and Okta Domain. Contact us at support@isolocity.com. (You can also edit this information within the Isolocity app if you have an existing Admin role.)
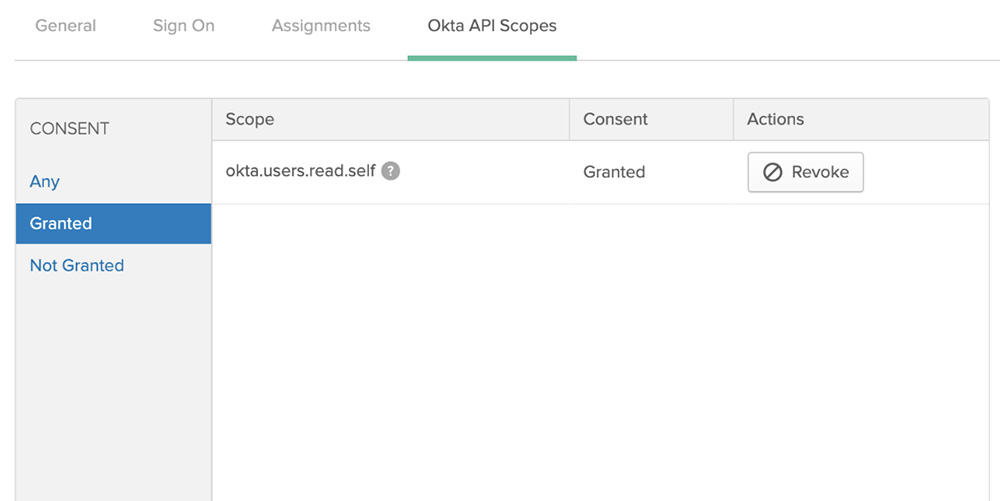
- Click the Okta API Scopes tab. Find okta.users.read.self and click Grant.
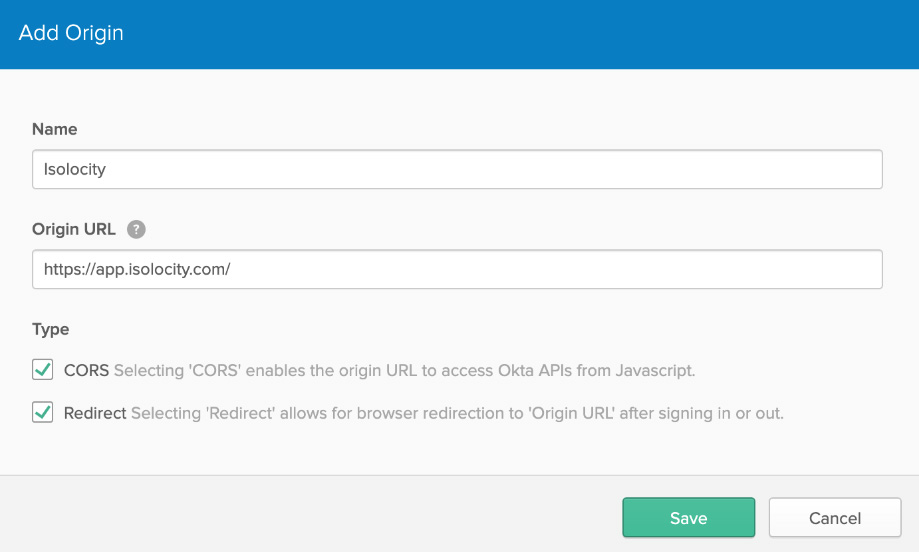
- Add the Isolocity url in API > Trusted Origins
- Allow groups to be included in the response. API > Authorization Servers > default > Claims > Add Claim
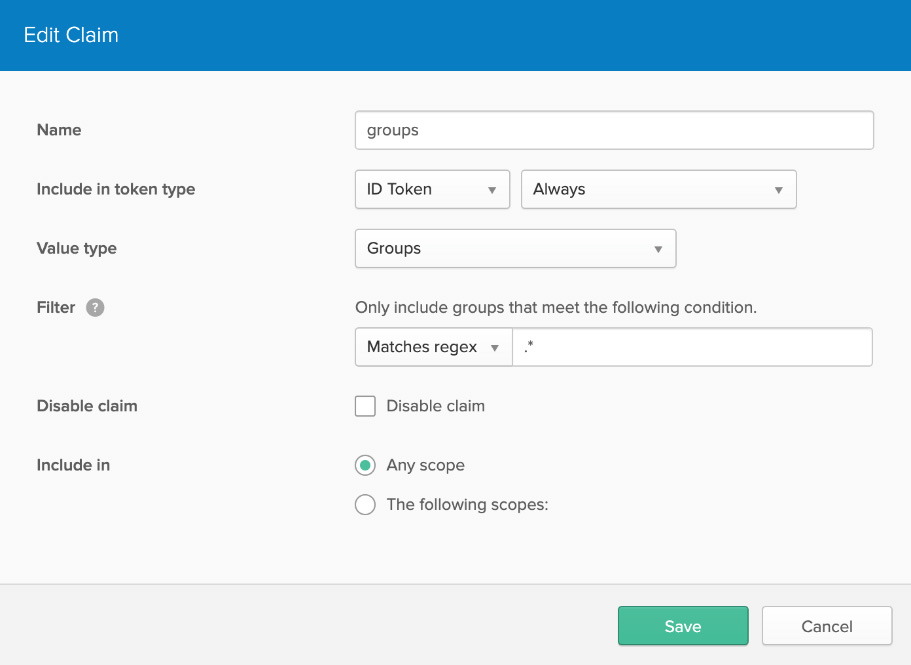
- Click Next, then enter the following information:
Isolocity Roles in Okta
Our app will recognize the following roles which you will need to set up as “Groups” in Okta. These roles are listed in decreasing order in terms of their capabilities within our app.
- Isolocity_Role_Admin
- Isolocity_Role_User (default)
- Isolocity_Role_Manager
- Isolocity_Role_Production
- Isolocity_Role_Employee
Once these “groups” are set up in Okta, assign them to your users.
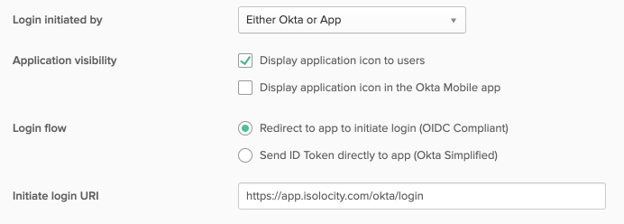
Isolocity on the Okta Dashboard
You can add our app to your Okta dashboard so your users can just click it there. Please set “Initiate login uri” to https://app.isolocity.com/okta/login as in the image below. Our logo is located at https://ibb.co/n65Qgwz